MODBUS PROTOCOL
After creation of
ICS Lab it's time to do some pentesting. I will start with Modicon Communication Bus - MODBUS. It's old, open, widely supported and unsecured protocol -
best place to start from for newbie ICS cybersecurity enthusiast like me. I don't see a point in writing here history and specification of MODBUS, because it is easily avaible
on internet(links below). But still I will write some notes-style informations for me to help with remembering and for reader for quick summary.
- Application layer messaging protocol
- Based on "request/reply" methodology
- Uses three protocol data units(PDU)
- Modbus Request
- Modbus Response
- Modbus Exception Response
- Master-Slave or Server-CLient based model
- No authentication
- No authorization
- No encryption
- Uses function codes which can be abused
SCENARIO
I'm using virtualized ICS lab descripted in a
previous post.
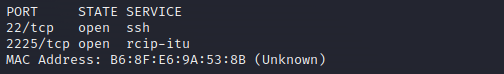
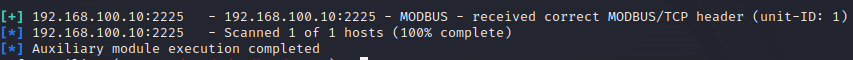
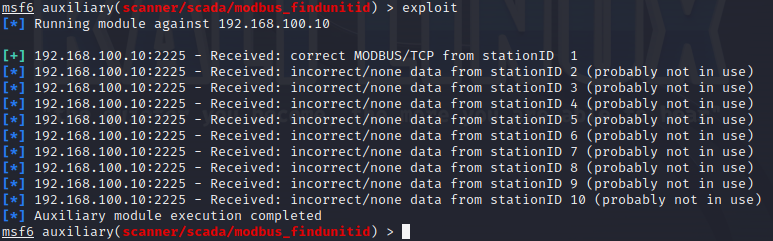
Let's assume that hacker has a access to cabled network via switch (without locked free ports) but nothing else.
Attacker has a laptop with Kali Linux OS. No hardware sniffing tools/network taps.
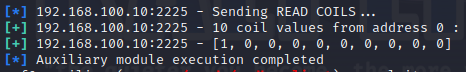
GOAL: Disrupt the work of the assembly line